Building Secure Cross-Chain Infrastructure
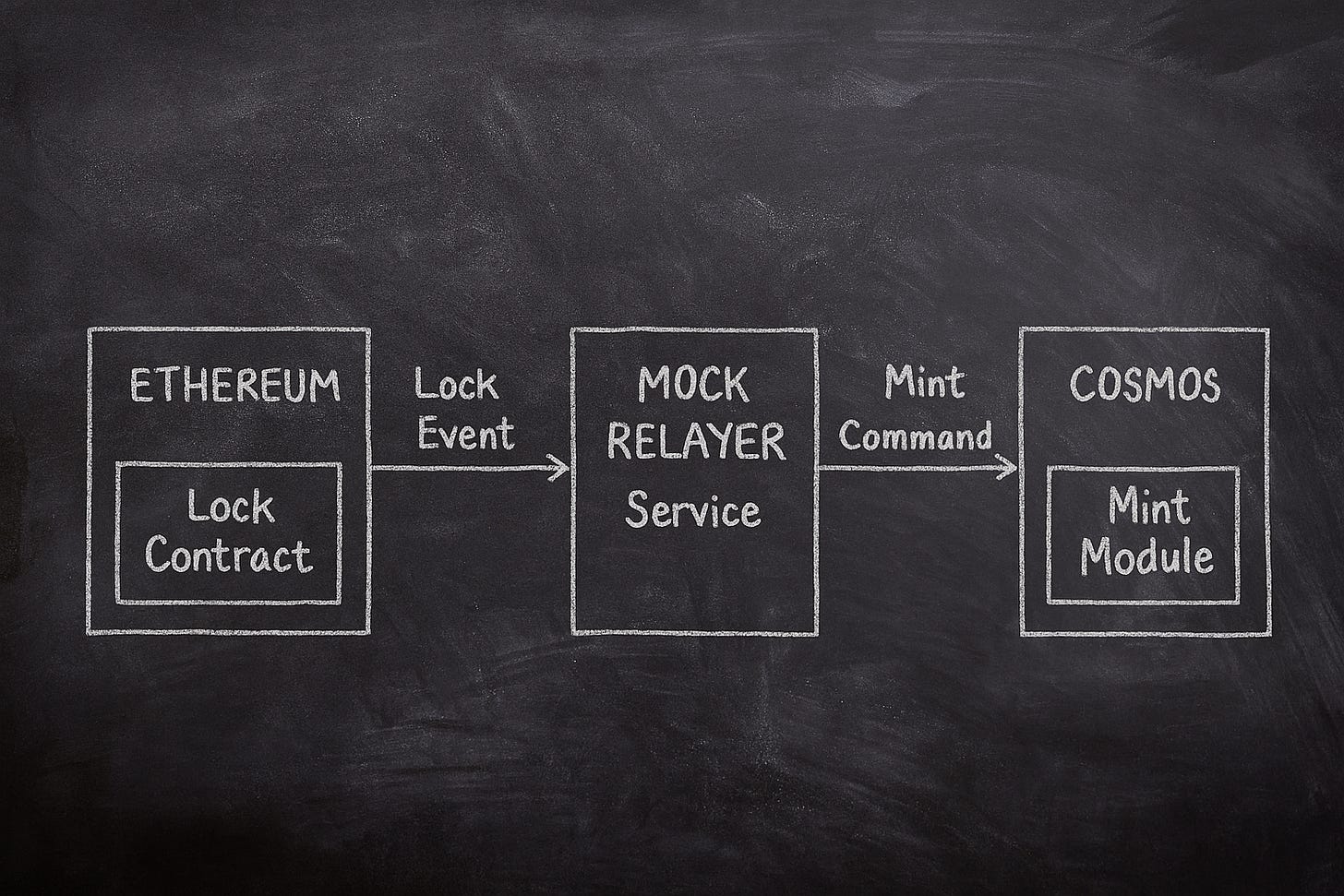
A simple experiment for moving tokens between chains.
Blockchain has fragmented into a multi-chain reality with over $108 billion in DeFi value locked across 200+ networks, creating both unprecedented opportunities and critical security challenges. Cross-chain bridge exploits have stolen $2.8 billion since 2022, representing 40% of all Web3 hacks. Meanwhile, $50 billion in value has transferred through LayerZero protocols alone, demonstrating massive demand for interoperability solutions.
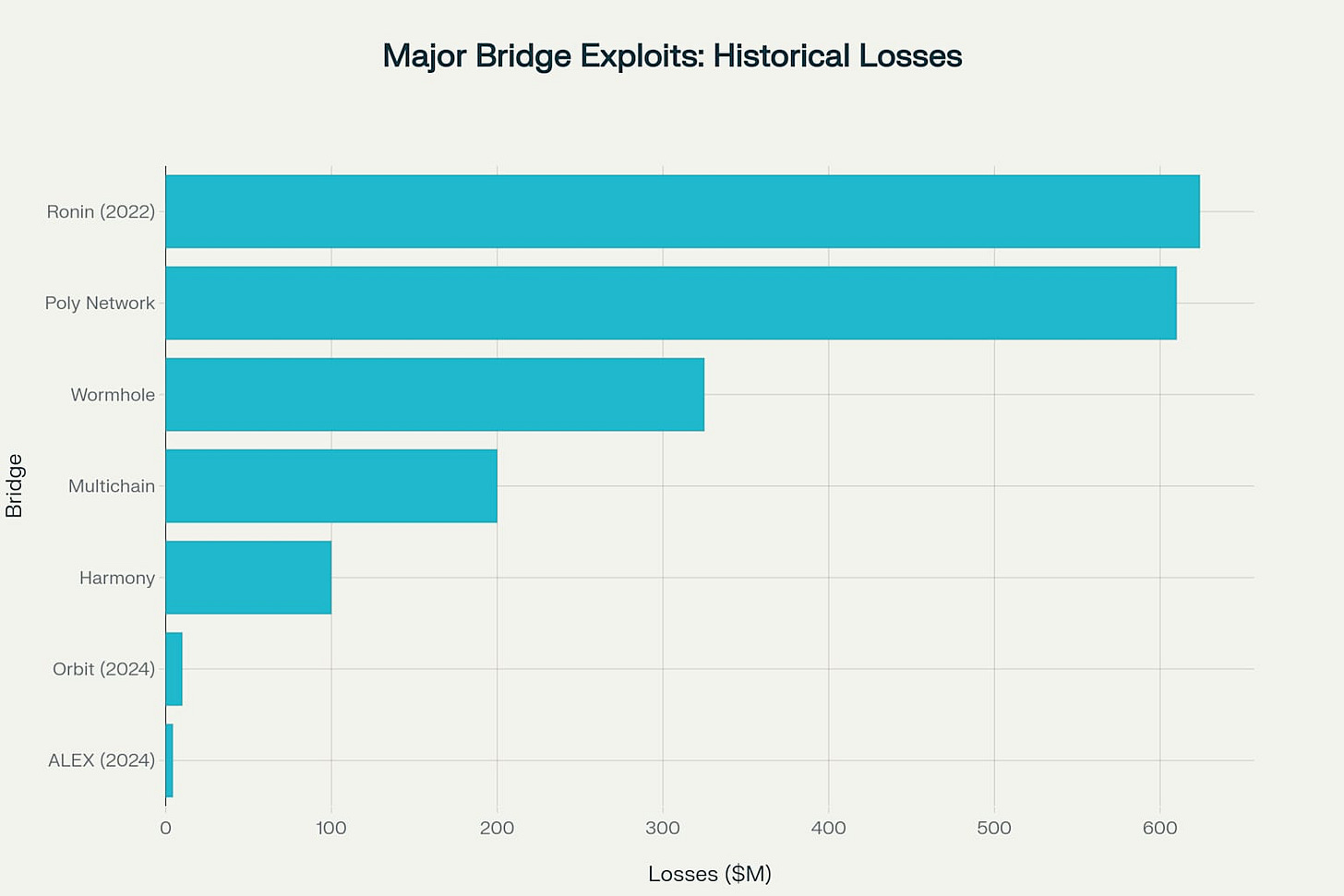
Historical Context of Major Exploits
The scale of historical bridge exploits underscores the critical importance of security improvements. The Ronin Bridge exploit of 2022, resulting in $624 million in losses, remains the largest bridge hack in history. These incidents have shaped current security practices and informed the development of more robust bridge architectures.
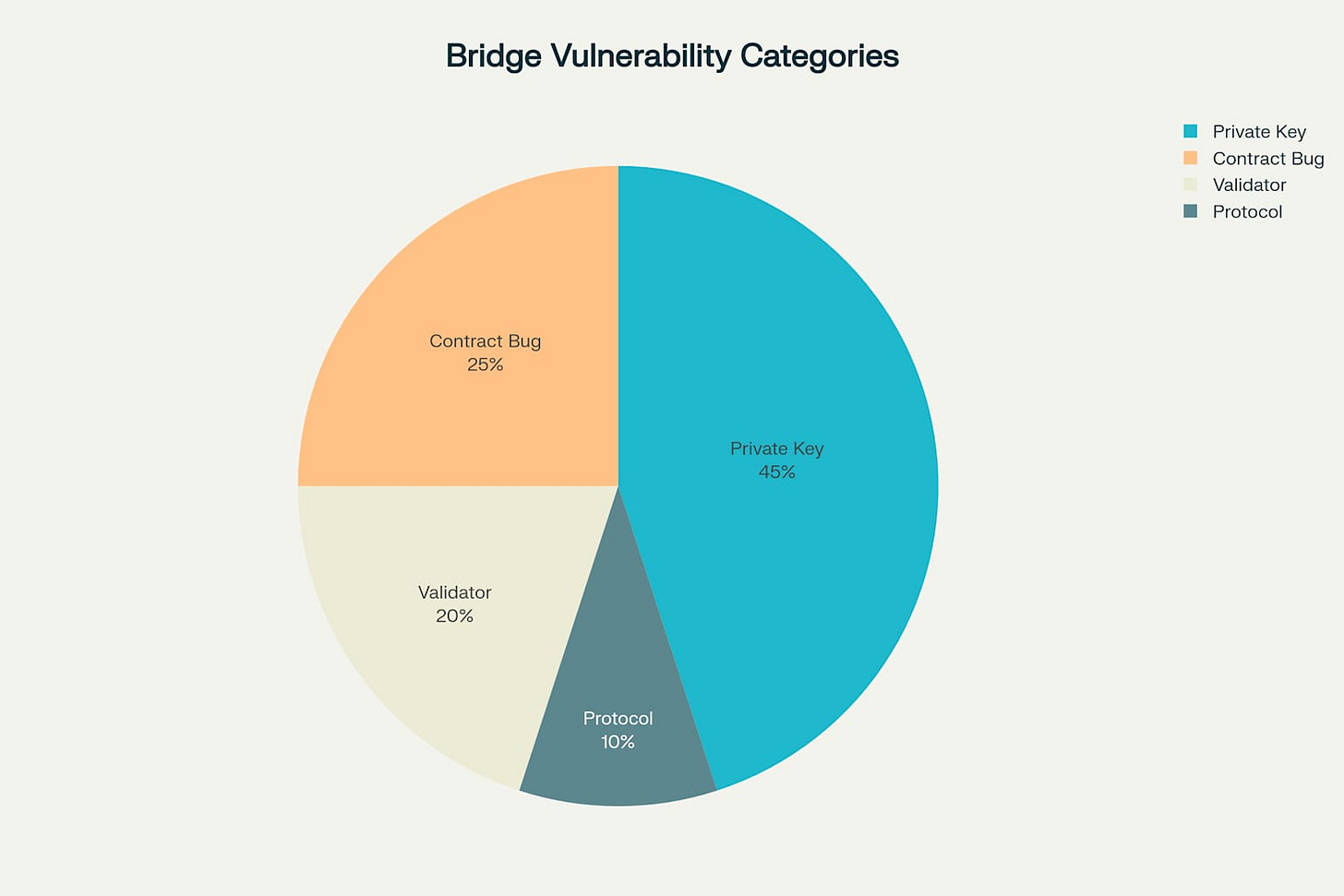
Vulnerability Categories
Understanding the root causes of bridge exploits reveals that private key compromise accounts for nearly half of all incidents. Smart contract vulnerabilities and validator takeovers represent additional significant risk factors.
This analysis examines a cross-chain token implementation that addresses these vulnerabilities through defense-in-depth security, event-driven architecture, and simplified developer experience.
Understanding Why Bridges Fail
After analyzing major bridge exploits, clear patterns emerge:
The Honeypot Effect: Traditional bridges concentrate billions in multisig wallets, creating irresistible targets. The Ronin bridge held over $600 million when attacked.
Validator Vulnerabilities: Most bridges rely on validator sets that directly control user funds. When 5 of Ronin's 9 validators were compromised through social engineering, the game was over.
Complexity Cascade: The Wormhole exploit originated from a signature verification bug in one of the many complex components. More code means more attack surface.
Detection Delays: Perhaps most concerning, these exploits often go unnoticed for days. Ronin's six-day detection window allowed attackers to extract maximum value.
A Different Architectural Approach
Instead of adding more complexity to address these issues, this analysis takes the opposite approach. The architecture separates concerns to eliminate entire categories of vulnerabilities:
Relayers should observe but never control funds. Even if every relayer is compromised, user funds remain secure in smart contracts with immutable logic.
Security Through Simplicity
The core locking mechanism demonstrates this philosophy:
function lockTokens(
uint256 amount,
string calldata cosmosAddress
) external nonReentrant whenNotPaused returns (uint256 lockId) {
require(amount >= MIN_LOCK_AMOUNT, "CrossChainBridge: amount too small");
require(amount <= MAX_LOCK_AMOUNT, "CrossChainBridge: amount too large");
require(_isValidCosmosAddress(cosmosAddress), "CrossChainBridge: invalid cosmos address format");
// Transfer tokens from user to bridge
token.safeTransferFrom(msg.sender, address(this), amount);
// Update state
lockedBalances[msg.sender] += amount;
totalLocked += amount;
lockId = ++_lockIdCounter;
// Emit event for relayer consumption
emit TokensLocked(msg.sender, cosmosAddress, amount, lockId);
}This function does exactly three things:
Validates inputs to prevent user errors
Transfers tokens to the contract
Emits an event for cross-chain coordination
No complex validator logic. No external dependencies. Apparently, no opportunities for unexpected interactions.
Defense in Depth
While simplicity should be the primary defense, here, there are multiple security layers:
contract CrossChainBridge is ReentrancyGuard, Pausable, Ownable {
using SafeERC20 for IERC20;
// Prevent dust attacks and limit exposure
uint256 public constant MIN_LOCK_AMOUNT = 1e15; // 0.001
uint256 public constant MAX_LOCK_AMOUNT = 1000000e18; // 1M
ReentrancyGuard: Prevents the recursive calling patterns that have drained numerous DeFi protocols.
Pausable: Provides an emergency stop mechanism—critical for incident response.
Amount Bounds: Limits both dust attacks and maximum exposure per transaction.
SafeERC20: Handles non-standard token implementations that have caused issues in other bridges.
Addressing User Experience
Technical security means nothing if users make preventable errors. We've seen millions lost to incorrect addresses, so here is a naive but practical Cosmos validation:
function _isValidCosmosAddress(string calldata cosmosAddress) internal pure returns (bool) {
bytes memory addr = bytes(cosmosAddress);
// Cosmos addresses have specific length requirements
if (addr.length < 39 || addr.length > 59) {
return false;
}
// Verify the "cosmos" prefix
if (addr.length >= 6) {
return (
addr[0] == 'c' && addr[1] == 'o' && addr[2] == 's' &&
addr[3] == 'm' && addr[4] == 'o' && addr[5] == 's'
);
}
return false;
}
This validation catches common errors:
Ethereum addresses mistakenly used for Cosmos destinations
Truncated addresses from copy-paste errors
Completely malformed inputs
While not exhaustive, it prevents the majority of user mistakes we've observed in production bridges.
Comprehensive Testing Strategy
Security isn't just about code—it's about confidence in that code. The test suite covers something like 35+ scenarios:
describe("CrossChainBridge", function () {
it("Should successfully lock tokens", async function () {
const tx = await bridge.connect(user1).lockTokens(LOCK_AMOUNT, COSMOS_ADDRESS);
await expect(tx)
.to.emit(bridge, "TokensLocked")
.withArgs(user1.address, COSMOS_ADDRESS, LOCK_AMOUNT, 1);
// Verify state changes
expect(await bridge.getTotalLocked()).to.equal(LOCK_AMOUNT);
});
it("Should handle edge cases gracefully", async function () {
// Test minimum amounts, maximum amounts, invalid addresses
await expect(
bridge.connect(user1).lockTokens(tooSmallAmount, COSMOS_ADDRESS)
).to.be.revertedWith("CrossChainBridge: amount too small");
});
});
Testing Strategy: Beyond Unit Tests
Comprehensive testing for cross-chain systems requires specialized approaches:
Cross-Chain Integration Testing
Using frameworks like Hardhat's mainnet forking, here is a simulation of the complete flow:
describe("Cross-Chain Integration", function() {
it("Should handle complete lock-unlock cycle", async function() {
// 1. Lock on Ethereum
const lockTx = await bridge.lockTokens(amount, cosmosAddress);
const lockReceipt = await lockTx.wait();
// 2. Simulate relayer detecting event
const lockEvent = parseLockEvent(lockReceipt);
// 3. Generate Cosmos mint proof
const mintProof = await generateCosmosProof(lockEvent);
// 4. Execute unlock with proof
await bridge.executeUnlock(
mintProof.lockId,
user.address,
mintProof.amount,
mintProof.signature
);
// 5. Verify end state
expect(await token.balanceOf(user.address)).to.equal(initialBalance);
});
});
Fuzzing & Edge Cases
Echidna for property-based testing:
// Invariant: total locked must equal sum of individual locks
function echidna_balance_consistency() public view returns (bool) {
uint256 calculated = 0;
for (uint i = 0; i < users.length; i++) {
calculated += lockedBalances[users[i]];
}
return calculated == totalLocked;
}
// Invariant: bridge token balance >= total locked
function echidna_solvency() public view returns (bool) {
return token.balanceOf(address(this)) >= totalLocked;
}
Formal Verification
For critical functions, I'd use symbolic execution tools like Manticore or Mythril:
# Verify no integer overflow in lock amounts
@symbolic(amount="uint256")
def test_no_overflow(amount):
initial_locked = contract.totalLocked()
contract.lockTokens(amount, cosmos_address)
assert contract.totalLocked() >= initial_locked
Addressing the $2.8 Billion Problem: A Comprehensive Defense
Let's examine how this hardened design mitigates each major vulnerability category that has plagued bridges:
Honeypot Mitigation:
Smart contracts hold funds with immutable logic
Daily volume caps limit maximum exposure
Multi-sig admin prevents single-point compromise
Validator Isolation:
Relayers can only read events, never access funds
Unlock operations require cryptographic proofs
Replay protection prevents duplicate processing
Complexity Reduction:
Three components with single responsibilities
Clear separation between observation and execution
Standard patterns (CEI) prevent reentrancy
Real-time Monitoring:
Anomaly detection events for automated response
Comprehensive logging for forensic analysis
Integration with standard monitoring stacks
Example Attack Mitigation:
// Scenario: Compromised relayer attempts unauthorized unlock
function executeUnlock(...) external onlyRelayer {
// ✓ Relayer role limits who can call
// ✓ Signature verification ensures request originated from Cosmos
// ✓ Replay protection prevents reusing valid requests
// ✓ Daily limits cap maximum damage
// ✓ Monitoring alerts on unusual patterns
}
Gas Economics and Practical Considerations
Transaction costs matter for adoption:
Lock operation: ~120,000 gas (including ERC20 transfer)
At 30 gwei: ~$10 on Ethereum mainnet
L2 deployment: ~$0.10-0.50 per transaction
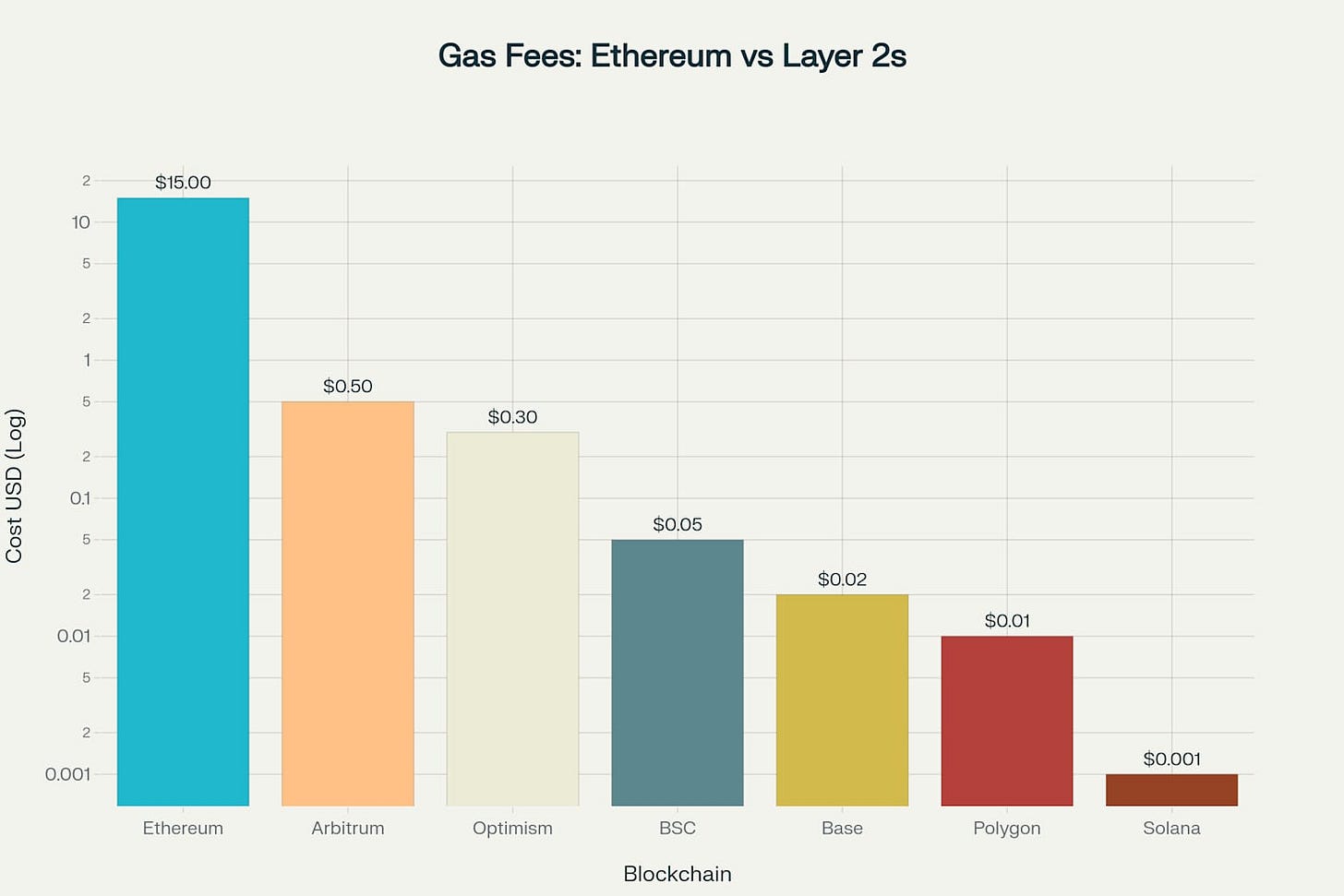
While not the absolute cheapest, the security benefits justify the costs. More importantly, the simple architecture makes gas optimization straightforward.
Developer Integration
I've prioritized developer experience without compromising security:
// 1. Standard ERC20 approval
await token.approve(bridge.address, amount);
// 2. Lock tokens with destination
await bridge.lockTokens(amount, "cosmos1abc...");
// 3. Monitor events
bridge.on("TokensLocked", (sender, destination, amount, lockId) => {
// Handle cross-chain coordination
console.log(`Lock ${lockId}: ${amount} tokens to ${destination}`);
});
No complex SDKs. No version dependencies. Just standard Web3 patterns that any dev understands.
Production Hardening: From PoC to Battle-Ready
While this implementation provides a quite secure foundation, production deployment demands additional defensive layers based on lessons from $2.8B in bridge exploits:
Multi-Signature Governance
Production deployment replaces single ownership with role-based access control:
contract CrossChainBridge is AccessControl {
bytes32 public constant GOVERNOR_ROLE = keccak256("GOVERNOR_ROLE");
bytes32 public constant GUARDIAN_ROLE = keccak256("GUARDIAN_ROLE");
bytes32 public constant RELAYER_ROLE = keccak256("RELAYER_ROLE");
constructor(address multiSig) {
_setupRole(DEFAULT_ADMIN_ROLE, multiSig);
_setupRole(GOVERNOR_ROLE, multiSig);
// Guardians can pause but not unpause
_setupRole(GUARDIAN_ROLE, multiSig);
}
function updateDailyLimit(uint256 newLimit)
external
onlyRole(GOVERNOR_ROLE)
{
require(newLimit > 0 && newLimit <= 10_000_000e18, "Invalid limit");
MAX_DAILY_VOLUME = newLimit;
emit DailyLimitUpdated(newLimit);
}
function emergencyPause() external onlyRole(GUARDIAN_ROLE) {
_pause();
emit EmergencyPause(msg.sender, block.timestamp);
}
}
Deploy with a 3-of-5 Gnosis Safe for GOVERNOR_ROLE and 2-of-7 for GUARDIAN_ROLE.
Secure Unlock Pattern with Cryptographic Proofs
The unlock mechanism implements defense-in-depth against replay and unauthorized access:
mapping(bytes32 => bool) public processedUnlocks;
function executeUnlock(
bytes32 proofId,
address recipient,
uint256 amount,
bytes calldata signature
) external onlyRole(RELAYER_ROLE) nonReentrant whenNotPaused {
// Prevent replay attacks
require(!processedUnlocks[proofId], "Bridge: already processed");
// Verify cryptographic proof from Cosmos
bytes32 message = keccak256(abi.encodePacked(
proofId,
recipient,
amount,
block.chainid
));
address signer = message.toEthSignedMessageHash().recover(signature);
require(hasRole(VALIDATOR_ROLE, signer), "Bridge: invalid signature");
// Mark as processed BEFORE transfer (CEI pattern)
processedUnlocks[proofId] = true;
totalLocked -= amount;
lockedBalances[recipient] -= amount;
// Execute transfer last
token.safeTransfer(recipient, amount);
emit TokensUnlocked(recipient, amount, proofId, block.timestamp);
}
Circuit Breaker with Graduated Response
Beyond simple pausing, implement intelligent threat response:
enum SecurityLevel { NORMAL, ELEVATED, CRITICAL }
SecurityLevel public currentLevel = SecurityLevel.NORMAL;
function updateSecurityLevel(SecurityLevel level)
external
onlyRole(GUARDIAN_ROLE)
{
currentLevel = level;
if (level == SecurityLevel.ELEVATED) {
MAX_DAILY_VOLUME = MAX_DAILY_VOLUME / 2; // 50% reduction
MAX_LOCK_AMOUNT = MAX_LOCK_AMOUNT / 2;
} else if (level == SecurityLevel.CRITICAL) {
_pause();
MAX_DAILY_VOLUME = MAX_DAILY_VOLUME / 10; // 90% reduction
}
emit SecurityLevelChanged(level, block.timestamp);
}
Fee Mechanism for Sustainability
A minimal fee structure ensures relayer incentives and protocol sustainability:
uint256 public constant BRIDGE_FEE_BPS = 10; // 0.1%
uint256 public accumulatedFees;
function lockTokens(uint256 amount, string calldata cosmosAddress) external {
uint256 fee = (amount * BRIDGE_FEE_BPS) / 10000;
uint256 netAmount = amount - fee;
// Fee accumulation for relayers
accumulatedFees += fee;
// Lock net amount
_executeLock(netAmount, cosmosAddress);
}
function claimRelayerFees() external onlyRole(RELAYER_ROLE) {
uint256 fees = accumulatedFees;
accumulatedFees = 0;
token.safeTransfer(msg.sender, fees);
}
Moving Forward
The cross-chain future isn't about building the most sophisticated bridge—it's about building bridges that don't make headlines for the wrong reasons. This implementation represents a simple experiment for moving tokens between chains.
As the industry matures, we need infrastructure that prioritizes security and reliability over feature lists and marketing claims. The $2.8 billion in losses shows the cost of getting this wrong. Let's build bridges that last.
Full source code is available here https://github.com/boulder225/cross-chain-token